Introduction
DNSSEC signing lets DNS resolvers validate that a DNS response has not been tampered with. When you enable DNSSEC signing, Route 53 automatically creates a key-signing key (KSK) for you, based on the customer-managed customer master key (CMK) in AWS Key Management Service (AWS KMS) that you choose. The KSK is a cryptographic public-private key pair that signs the DNSKEY. The process is completed by creating a Delegation Signer (DS) record for the parent zone of the zone. This creates the required chain of trust for the hosted zone.
Using DNSSEC increases trust between the user and the target AWS account. It ensures that the integrity of the DNS record has not been tampered with and users are receiving information from the correct source. In the absence of DNSSEC, some network applications may warn that the response is not cryptographically signed which could lower the trust that the user has with the application resulting in potential customer churn owing to compliance, regulatory requirements or based on the lowered trust with the system.
In this article we will take a look at how we can enable DNSSEC signing in AWS Route53.
Note: Before you enable DNSSEC signing, make sure you read the pre-requisites and prepare for enabling DNSSEC signing to minimise the risk of zone outages.
Enable DNSSEC signing in AWS Route53
Following are the steps to enable DNSSEC signing in AWS Route53:
-
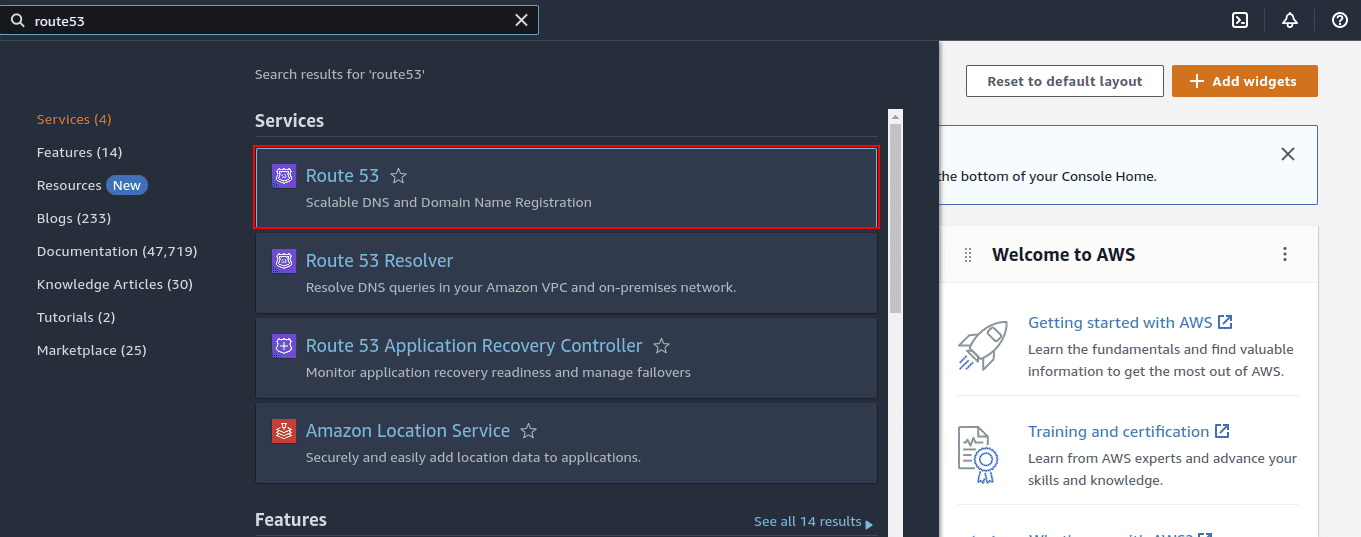
Login to the AWS Management Console and navigate to Route53
-
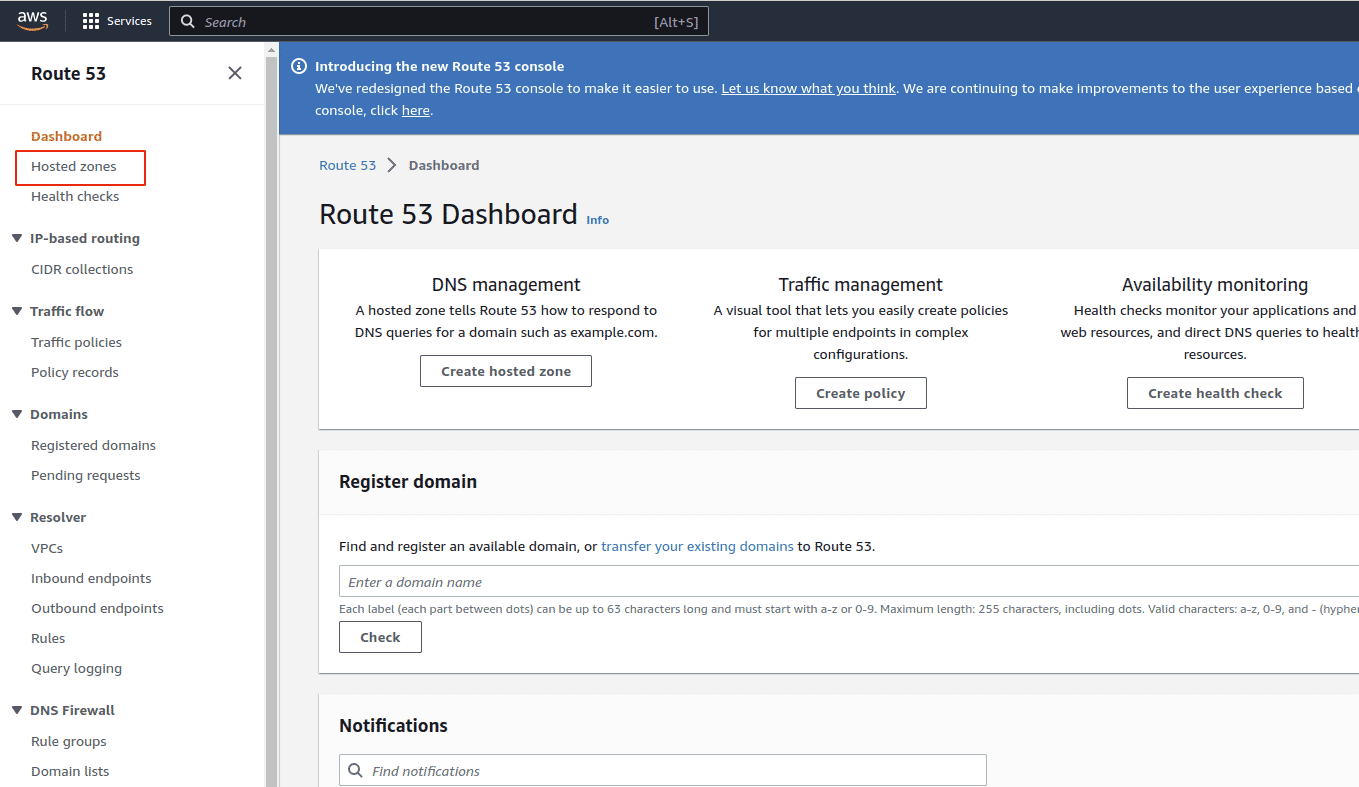
Under Dashboard, click Hosted Zones in the left navigation panel
-
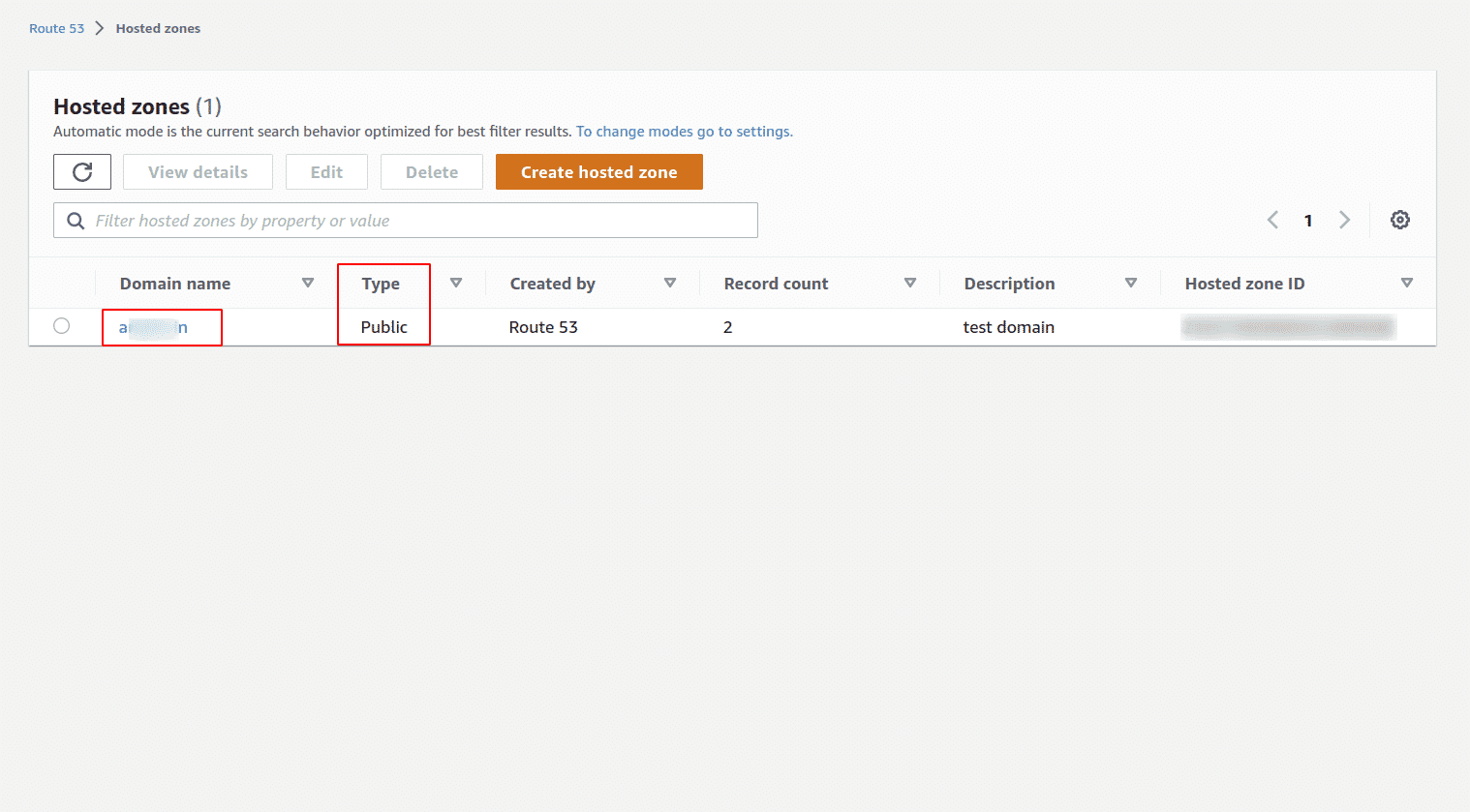
Click on the domain name of the public-hosted zone that you want to reconfigure. A public Route 53 hosted zone has the Type set to Public
-
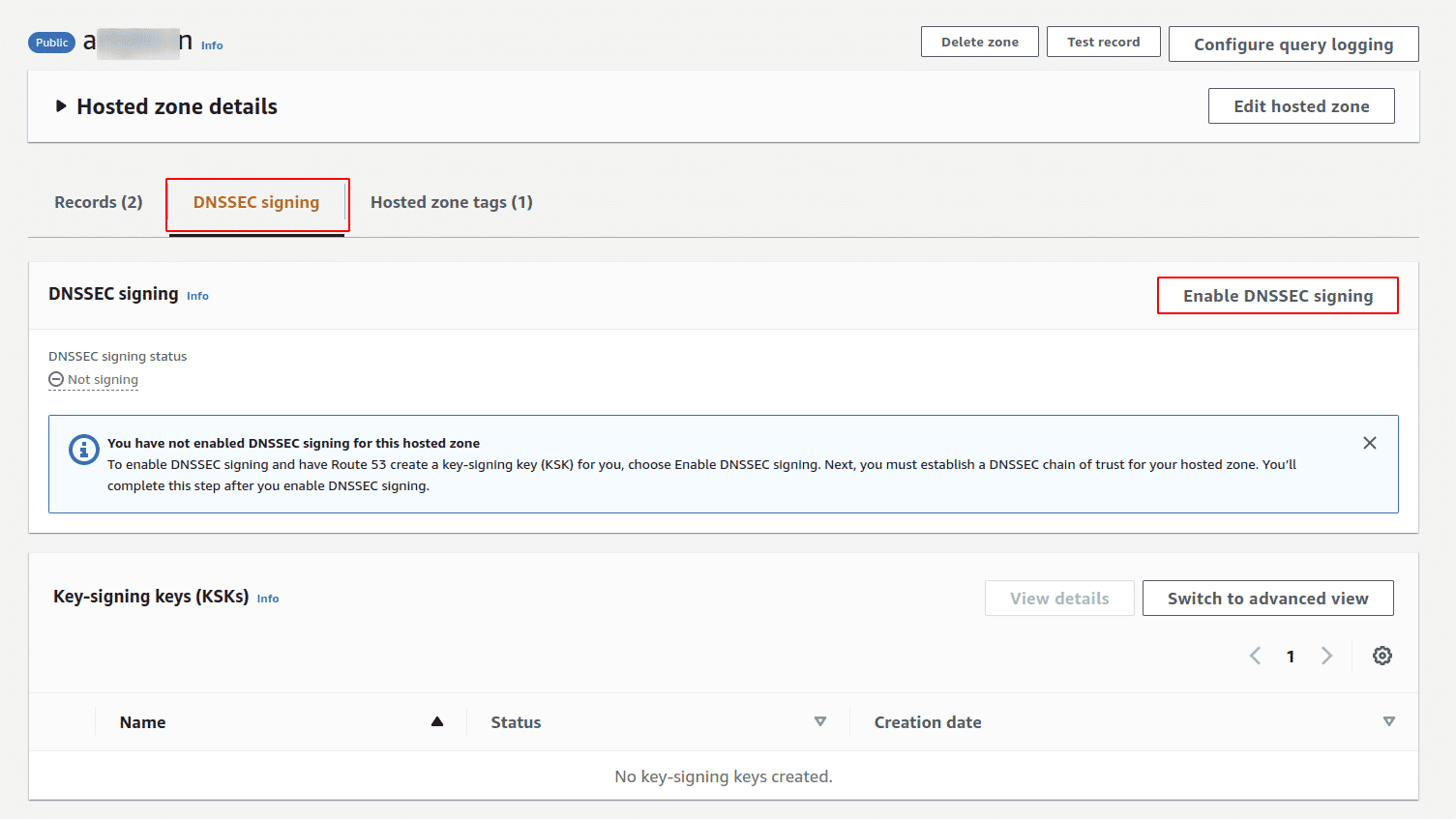
Select the DNSSEC signing tab and choose Enable DNSSEC signing
-
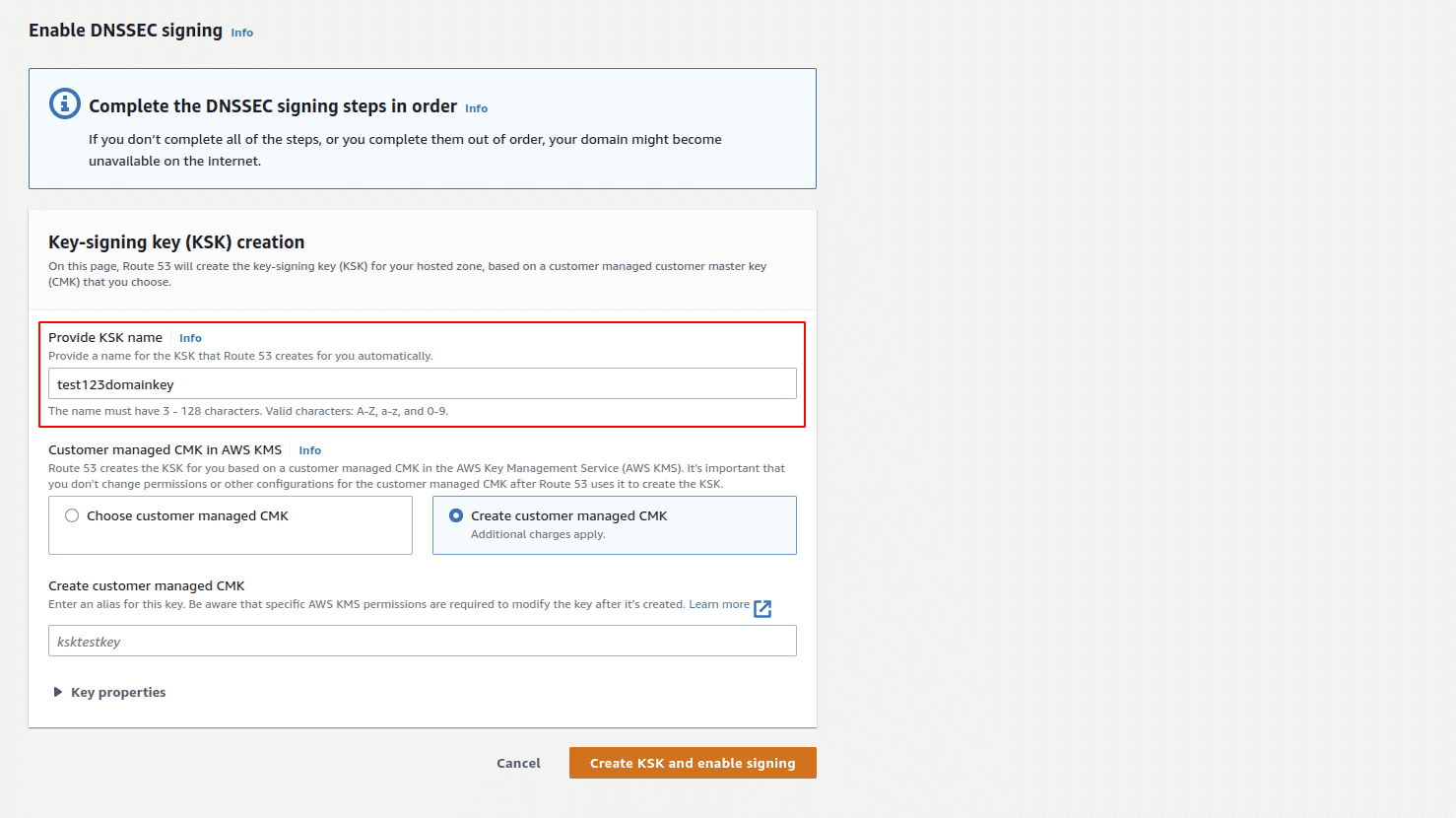
On the Enable DNSSEC signing configuration page, for Provide KSK name, enter an alphanumeric name for the KSK
-
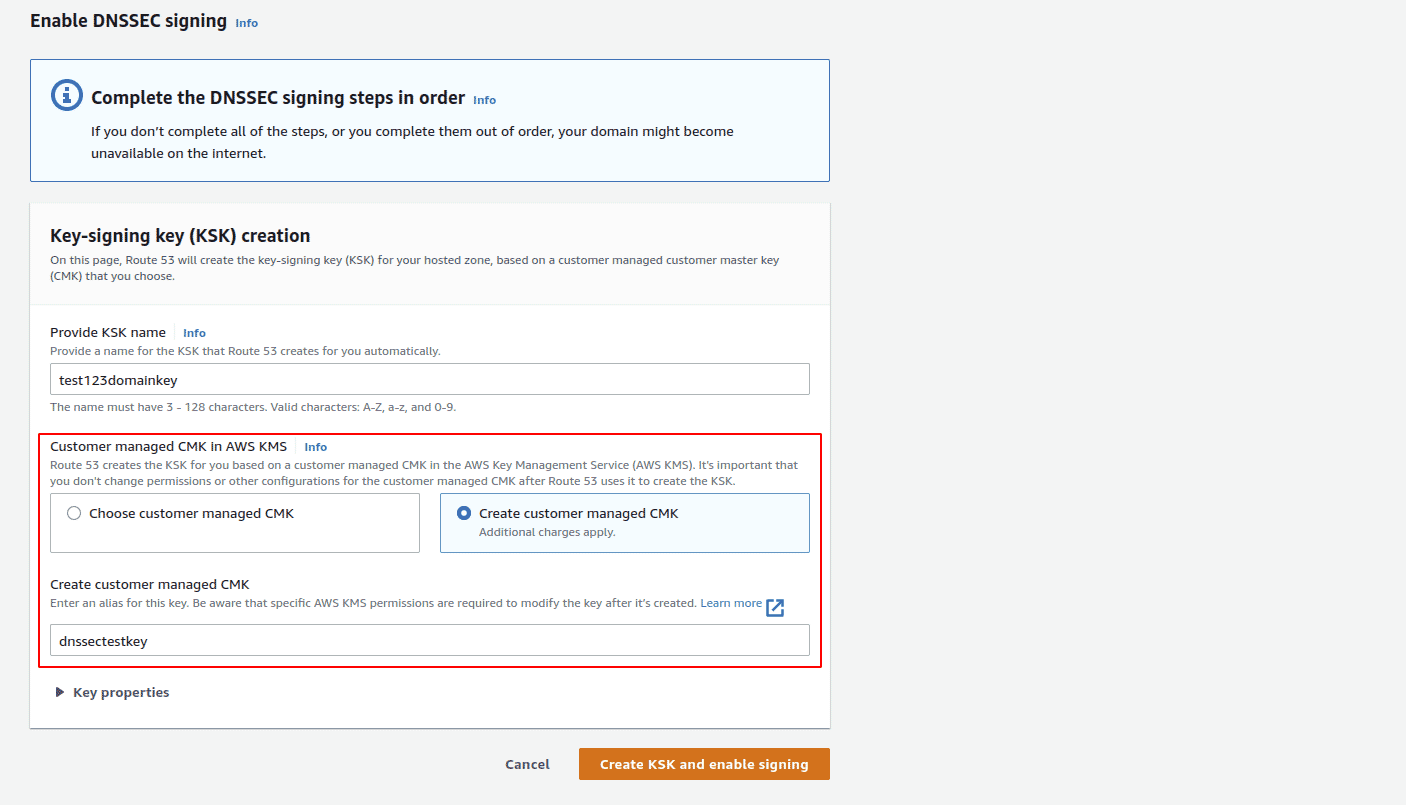
Under Customer managed CMK in AWS KMS, choose the customer-managed CMK for Amazon Route 53 to use when it creates the KSK for you. Select Choose customer managed CMK to use an existing customer-managed CMK that applies to DNSSEC signing or select Create customer managed CMK to create a new customer-managed CMK for DNSSEC signing
Note: Before providing the customer-managed CMK, make sure that it fulfills these requirements.
-
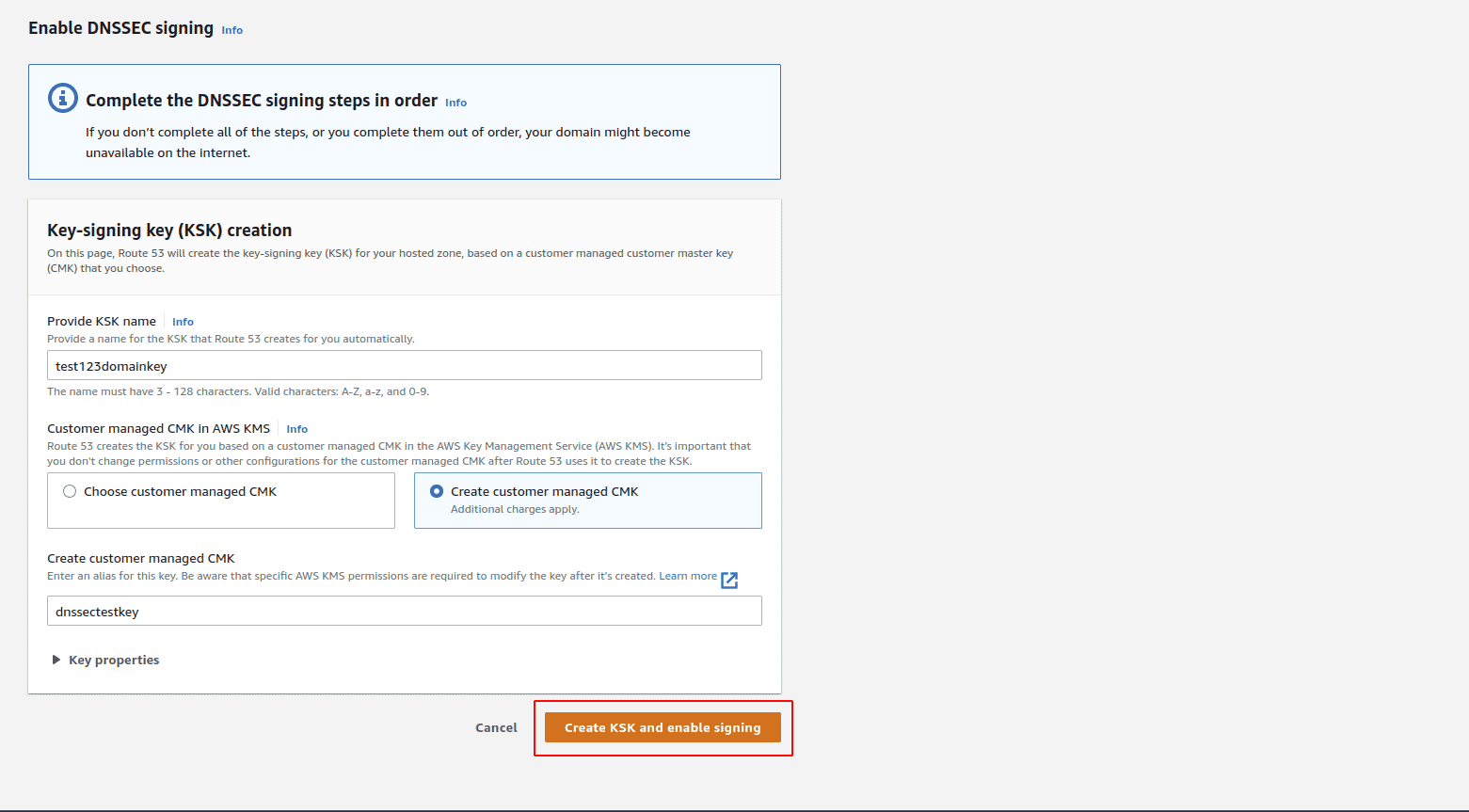
Click on Create KSK and enable signing to enable DNSSEC signing for the selected hosted zone
-
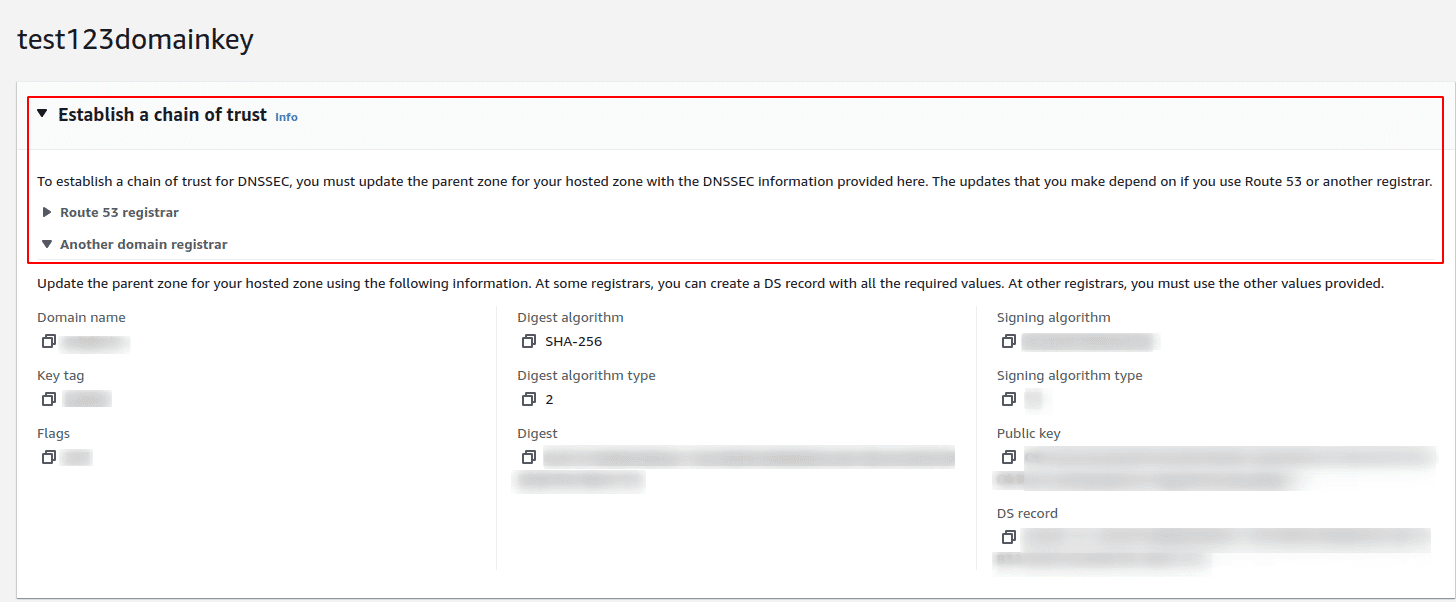
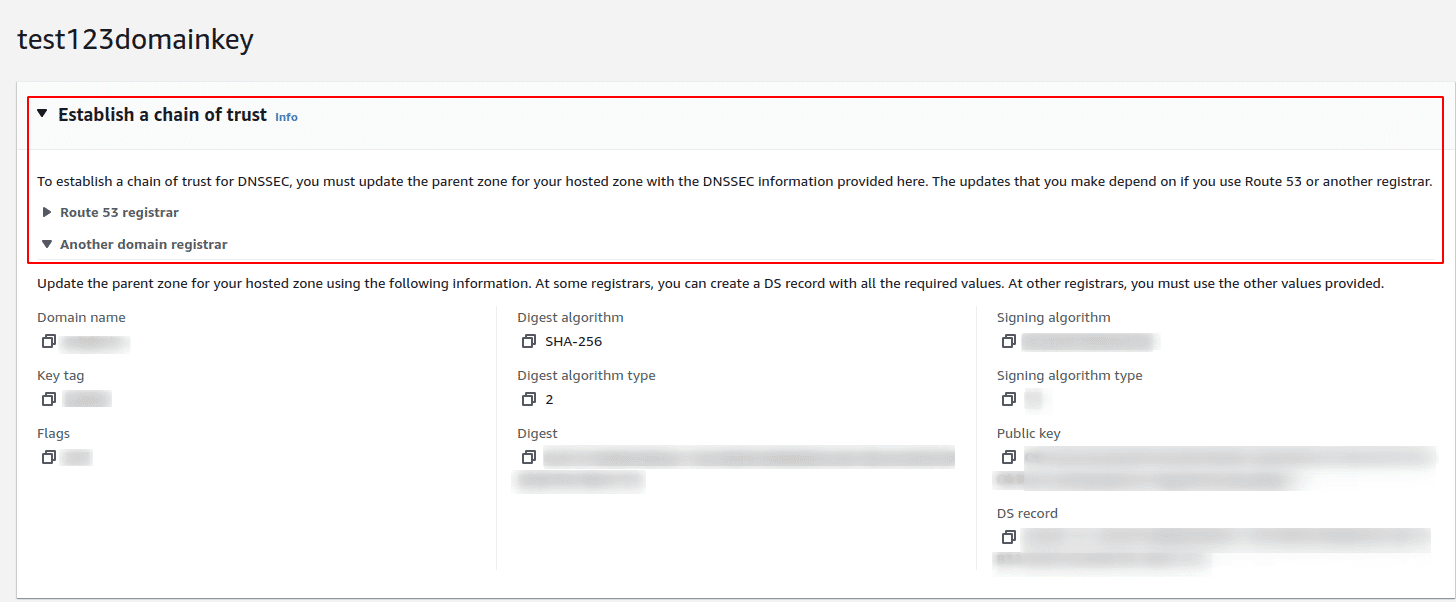
Once DNSSEC signin is enabled, under DNSSEC signing tab, click on View information to create DS record
-
Follow the instructions under Establish a chain of trust section to complete the DNSSEC signing setup for the hosted zone or follow this document from AWS for guidance on establishing a chain of trust

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.