Introduction
In the event of passwords being breached, a reused password can allow an attacker to take over a user account or compromise the entire AWS account.
Preventing password reuse increases account resiliency against brute force login attempts. AWS IAM password policies can prevent the reuse of a given password by the same user by enabling Prevent password reuse policy.
In the absence of this policy, there is no way to prevent users from reusing their old passwords after expiry or when password change operations are performed.
Here’s how you can enable Prevent Password Reuse policy on AWS via the console and CLI
Steps to enable Prevent Password Reuse policy via AWS console
https://www.youtube.com/watch?v=j4OO06TaQUs&t=17s
-
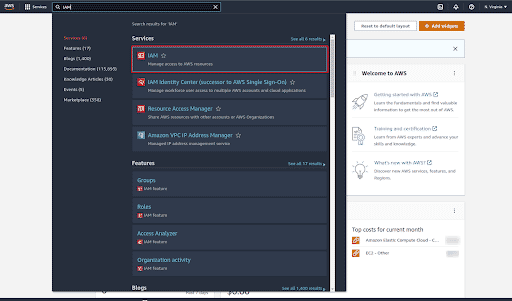
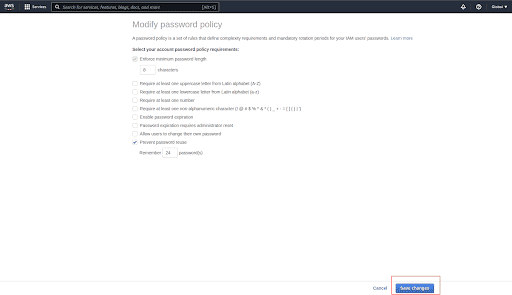
Sign in to the AWS Management console
-
Navigate to IAM service
-
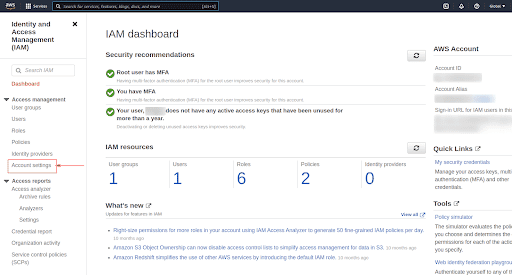
On the left menu, click on Account settings
-
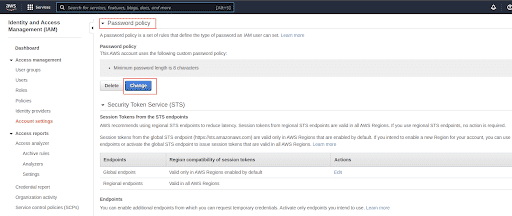
Under Password Policy section, click on Change password policy button
-
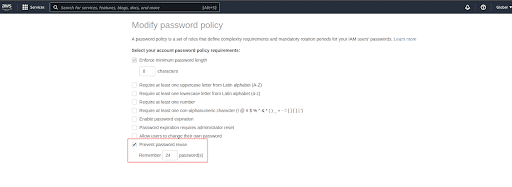
Check the Prevent password reuse checkbox
-
For the password history, we can set the value between 1 and 24. As per CIS benchmark we should set this value to 24 or you can set it up as per your organization’s policies and processes
-
Click on Save changes. This will enable the password policy to prevent reuse of old passwords
Steps to enable Prevent Password Reuse policy via AWS CLI
https://www.youtube.com/watch?v=QoYvhwoHSjA&t=2s
-
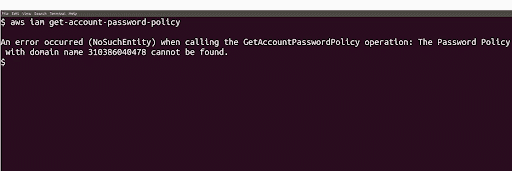
To check password policy manually, run get account password policy command
aws iam get-account-password-policy -
We can see that this policy has not been enabled yet
-
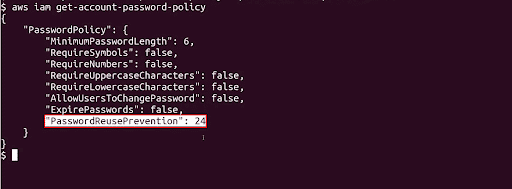
Run update account password policy command on your terminal with password reuse prevention parameter value set to an integer between 1 and 24
aws iam update-account-password-policy \ --password-reuse-prevention 24(As per CIS benchmark we should set this value to 24 or you can set it up as per your organization’s policies and processes)
-
To check if the policy has been updated, run the command in step 1 again

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.