Introduction
IPv6 was introduced as a replacement for IPv4 foreseeing the exhaustion of the IPv4 address space at some point in the future. IPv6 provides many security benefits by design. For instance, using some tools (and with the requisite bandwidth), an attacker could scan the entire public IPv4 address space in less than an hour. With IPv6 however, even when taking a very liberal estimate, a scan of all IPv6 addresses would take hundreds, possibly hundreds of thousands of years.
Many popular network scanners are used by sysadmins and SREs for scanning and discovery of IPv4 hosts and services within their network, whether for the purpose of inventorying the network or to spot security issues in the network. Since the adoption of IPv6 has started, sysadmins and SREs who would like to look into their IPv6 networks can take a look at some of the open source IPv6 scanners that we will be listing in this article.
Note: Make sure that the scans are conducted in the networks where you are allowed to do so with appropriate permissions.
5 tools for scanning IPv6 networks
When searching for tools and options for port scanning and host discovery for IPv6, you can definitely take a look at the following 5 tools. All the tools listed here for IP v6 scanning are open source.
-
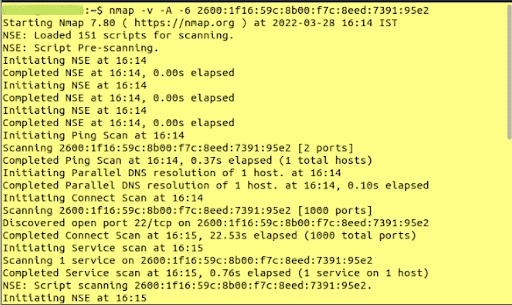
Nmap
Nmap is one of the most popular network scanners for discovering hosts and services on the network. Nmap has been used for scanning IPv4 networks for years, but did you know this tool also supports IPv6 scans? Yes! Nmap has support for IPv6 scans. All you need to do is supply ‘-6’ argument to scan an IPv6 network.
-
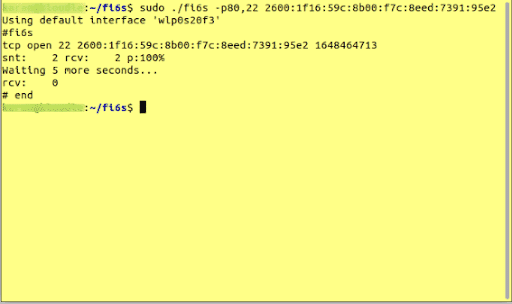
fi6s
fi6s is a fast port scanner for IPv6 networks written in C. fi6s makes use of its own TCP/IP stack to scan IPv6 networks with fast speed. A known limitation of fi6s is that it does not have support for all UDP protocols, and will only produce results when scanning for supported UDP protocols. Also from the github page it appears that this software is not maintained actively anymore, but if you are just looking to experiment with some tools, you can give it a try.
-
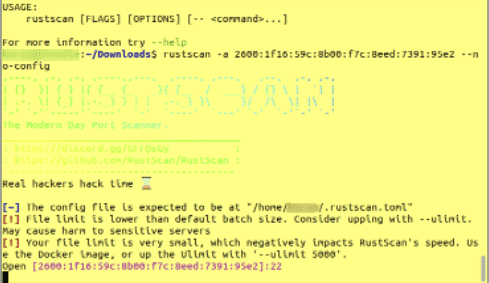
RustScan
RustScan is an extremely fast port scanner written in - as the name suggests - Rust. RustScan boasts the ability to scan all 65535 ports in 3 seconds, though the speed might also depend on the networking equipment available to you. Consumer networking devices might not be equipped for the bandwidth throughput required for achieving the scan speeds mentioned above.
-
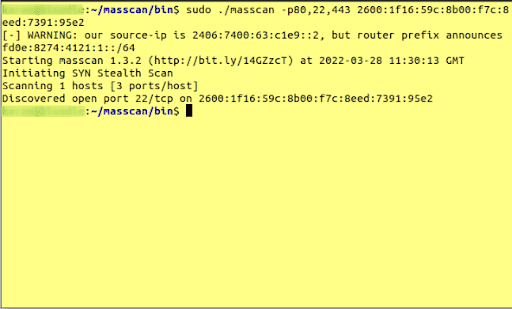
Masscan
Masscan is an Internet-wide port scanner written in C. This tool uses its own TCP/IP stack and is capable of sending 10 million packets per second (as long as the network and the machine does not limit the tool’s ability).
-
v6disc
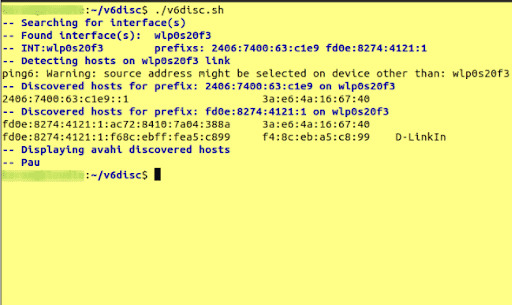
v6disc is different from all of the other tools mentioned so far, as it is used for host discovery and not port scanning. v6disc has dual-stack support which can be useful for mapping an IPv6 and IPv4 address pair to a particular host.
Conclusion
Since the adoption of IPv6 has started, it has become an interesting area to learn and understand IPv6 and its implementation. The tools mentioned in this list can be used to perform scans of IPv6 networks. When using “mass scanning” tools however (such as fi6s, Masscan or rustscan), specific considerations and techniques might need to be used for scans to be effective.
While there are a few addressing techniques and scanning methods that can be used to reduce the estimated scan time of IPv6 networks, widespread adoption of IPv6 still does bring with it certain changes to networking that have to be considered from a security perspective.

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.