Introduction
Prowler is a command line tool that helps you with AWS security assessment, auditing, hardening, and incident response.
It follows guidelines of the CIS Amazon Web Services Foundations Benchmark (49 checks) and has more than 190 additional checks related to GDPR, HIPAA, PCI-DSS, ISO-27001, FFIEC, SOC2, and others.
Pre-requisites?
Prowler can be installed on any Linux, Mac OS, or Windows with Cygwin or virtualization. Basic requirements include
- Install jq and detect-secrets to work properly.
- Python pip
- The latest version of AWS-CLI. It works with either v1 or v2, however latest v2 is recommended if using new regions since it requires an STS v2 token, and other components needed.
Steps to install
For Ubuntu Linux
-
Install pip
sudo apt install python3 python3-pip jq git zip -
Installation of detect-secrets
pip install detect-secrets==1.0.3 -
Install AWS CLI V2 and refer to the official documentation for other methods https://aws.amazon.com/cli/
curl "https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"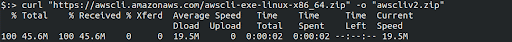
unzip awscliv2.zip sudo ./aws/install -
Now clone the prowler tool from GitHub
git clone https://github.com/prowler-cloud/prowler -
Before running the Prowler tool configure an AWS account on the terminal on which you want to run Prowler. For configuration refer to the documentation https://docs.aws.amazon.com/cli/latest/userguide/cli-configure-quickstart.html#cli-configure-quickstart-precedence
-
The above credentials that are configured must have proper permissions associated with a user or role to do all checks. Only adding the AWS-managed policies, SecurityAudit and ViewOnlyAccess, to the user or role being used will also work.
-
Once the Prowler tool is cloned, change to the prowler directory and run the tool.
./prowler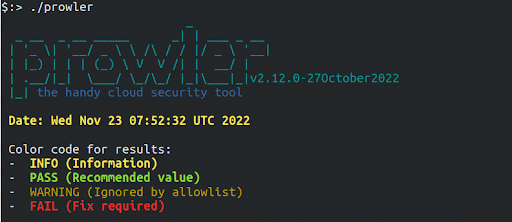
Reference: https://github.com/prowler-cloud/prowler

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.

Riyaz Walikar
Founder & Chief of R&D
Riyaz is the founder and Chief of R&D at Kloudle, where he hunts for cloud misconfigurations so developers don’t have to. With over 15 years of experience breaking into systems, he’s led offensive security at PwC and product security across APAC for Citrix. Riyaz created the Kubernetes security testing methodology at Appsecco, blending frameworks like MITRE ATT&CK, OWASP, and PTES. He’s passionate about teaching people how to hack—and how to stay secure.